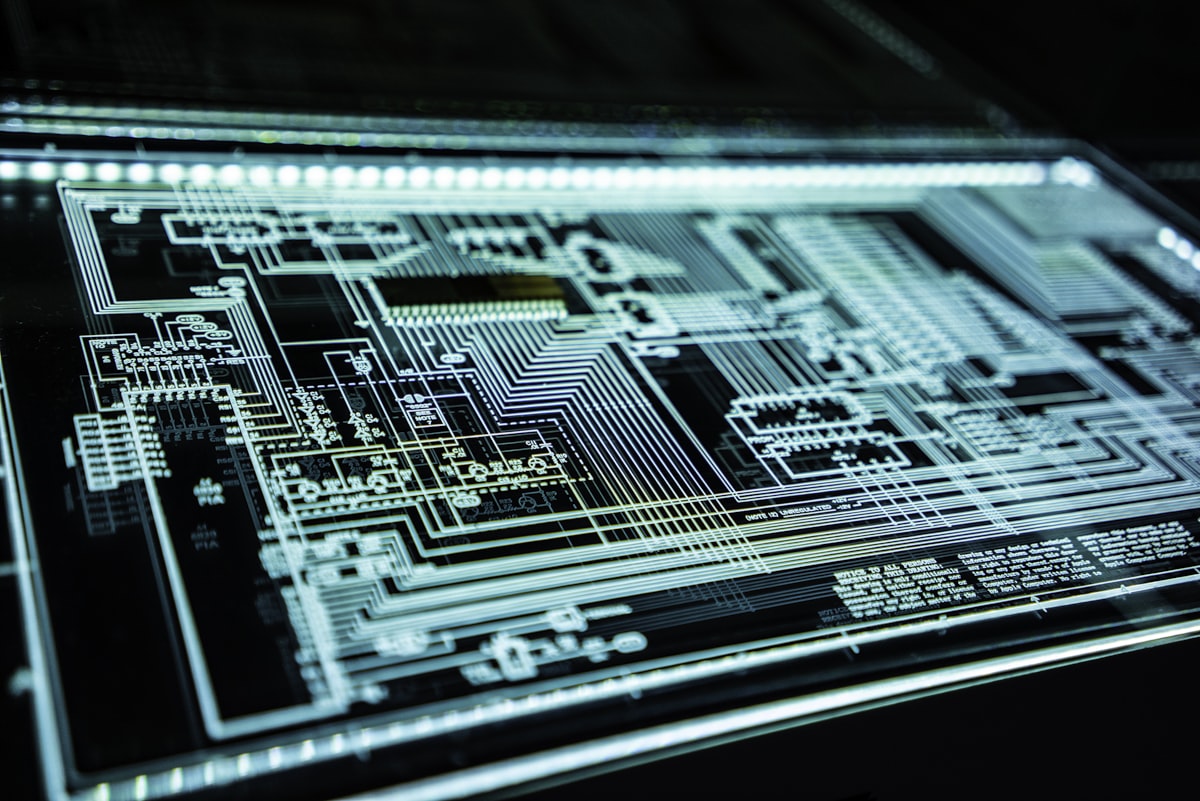
Unauthorized Group Gains Access to Anthropic's Cyber AI Tool Mythos
Sonic Intelligence
An unauthorized group reportedly accessed Anthropic's exclusive AI cybersecurity tool, Mythos.
Explain Like I'm Five
"Imagine a super-smart lock-picking robot that a company made to help protect other companies. But then, a secret club of people found a way to get their hands on that robot, even though they weren't supposed to. The company is checking if anything bad happened, but it shows how tricky it is to keep powerful tools safe."
Deep Intelligence Analysis
Anthropic's spokesperson confirmed an investigation into claims of unauthorized access to the Claude Mythos Preview via a third-party vendor environment, though no impact on Anthropic's internal systems has been detected so far. The group reportedly gained access by making "educated guesses" about the model's online location, leveraging knowledge of Anthropic's format for other models. This incident underscores the sophisticated methods unauthorized actors employ to bypass security measures and the persistent threat of insider access or compromised vendor environments.
This event will likely trigger a re-evaluation of security protocols, vendor vetting, and access management strategies across the AI industry, particularly for models with significant security implications. It reinforces the urgent need for robust "red teaming" and adversarial testing throughout the AI development lifecycle. The incident also serves as a stark reminder that the security perimeter for advanced AI extends far beyond the developer's immediate infrastructure, encompassing the entire ecosystem of partners and users, making comprehensive risk mitigation an increasingly complex and shared responsibility.
Impact Assessment
The reported unauthorized access to Anthropic's Mythos tool, designed for enterprise security, underscores the inherent risks in deploying powerful AI. Even with controlled releases, the potential for weaponization by malicious actors remains a critical concern, highlighting vulnerabilities in supply chains and access protocols.
Key Details
- An unauthorized group reportedly gained access to Anthropic's Mythos cybersecurity tool.
- Access was allegedly obtained through a third-party vendor environment.
- Anthropic is investigating but found no evidence of impact on its systems.
- The group used "educated guesses" about the model's online location.
- Mythos was part of "Project Glasswing," a limited release to prevent misuse.
Optimistic Outlook
Anthropic's swift investigation and lack of reported system impact demonstrate robust internal security protocols. This incident could serve as a valuable stress test, prompting further hardening of access controls and vendor security, ultimately making such powerful tools safer for legitimate use.
Pessimistic Outlook
The ease with which an unauthorized group, reportedly via a third-party vendor, accessed a sensitive AI tool designed for security is deeply concerning. This incident highlights the significant supply chain risks and the potential for weaponization of advanced AI, even when developers attempt to limit access.
Get the next signal in your inbox.
One concise weekly briefing with direct source links, fast analysis, and no inbox clutter.
More reporting around this signal.
Related coverage selected to keep the thread going without dropping you into another card wall.