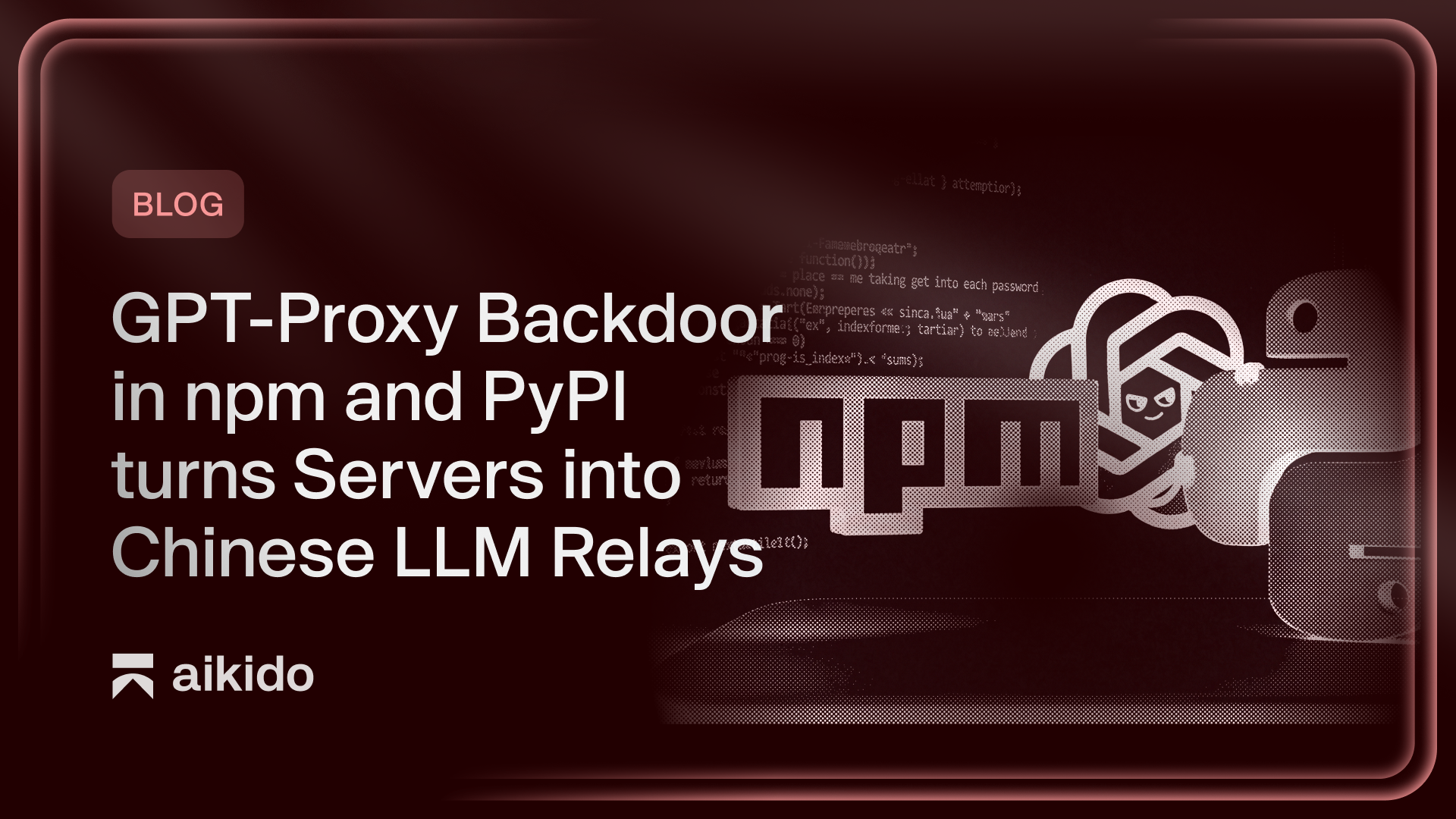
Malicious Packages Turn Kubernetes Servers into Covert LLM Proxies
Sonic Intelligence
Malicious npm and PyPI packages install a covert LLM proxy and reverse shells on Kubernetes servers.
Explain Like I'm Five
"Imagine you download a game, but secretly it also installs a hidden program that lets someone else use your computer to pretend they are you when talking to smart AI robots. It also tries to hide all its tracks super fast."
Deep Intelligence Analysis
The technical execution of this attack is notable for its multi-stage approach and operational sophistication. Initial droppers, delivered as Cython-compiled Python extensions or Node.js native addons, fetch more capable stage 2 binaries from GitHub. These binaries establish reverse tunnels to a Command and Control (C2) server, `sync.geeker.indevs.in`, granting attackers access to the LLM proxy, the victim's SSH server, and potentially HashiCorp Vault instances—a critical secrets store in Kubernetes. The malware employs process masquerading (`node-health-check --mode=daemon`) to blend in with legitimate system activity. Crucially, the droppers are programmed to erase all installation artifacts within two seconds of launching the stage 2 binary, including package directories and temporary files, severely hindering post-incident forensic efforts. The inclusion of an ngrok fallback in the npm variant further enhances the attacker's ability to maintain access by cycling through public endpoints.
The implications of this attack are far-reaching. Beyond the immediate compromise of Kubernetes infrastructure and potential data exfiltration, the establishment of covert LLM relays introduces a new vector for abuse. Attackers could leverage these relays to bypass rate limits, obscure their identity in AI-driven campaigns, or even facilitate the development of further malicious AI models. This incident underscores the critical vulnerability of software supply chains and the need for enhanced security measures, including rigorous package validation, runtime application self-protection (RASP), and advanced behavioral analytics to detect anomalous network traffic and process activity. Organizations must assume compromise and focus on resilient architectures that can detect and mitigate threats even when initial infection is stealthy, pushing for a shift from reactive forensics to proactive, real-time threat hunting.
Visual Intelligence
flowchart LR
A["Malicious Package"] --> B["Download Dropper"]
B --> C["Execute Binary"]
C --> D["Download Stage 2"]
D --> E["Install LLM Proxy"]
E --> F["Establish Tunnels"]
F --> G["Erase Evidence"]
G --> H["C2 Server"]
F --> H
Auto-generated diagram · AI-interpreted flow
Impact Assessment
This attack demonstrates a sophisticated supply chain compromise targeting critical infrastructure (Kubernetes) to establish covert LLM relay networks and gain deep access to sensitive systems. The rapid evidence erasure makes detection and forensics extremely challenging.
Key Details
- Two malicious packages, `kube-health-tools` (npm) and `kube-node-health` (PyPI), target Kubernetes environments.
- They silently install a full LLM proxy service on compromised machines.
- The droppers download stage 2 binaries from GitHub (e.g., `kube-diag-linux-amd64-packed`).
- The malware establishes reverse tunnels to attacker C2 server `sync.geeker.indevs.in` for LLM proxy, SSH, and HashiCorp Vault access.
- The npm variant includes an ngrok fallback for public endpoint exposure.
- Droppers actively erase evidence of execution within two seconds, deleting package directories and temporary files.
Optimistic Outlook
Prompt identification and analysis of such sophisticated threats by security researchers can lead to improved package repository scanning and enhanced runtime detection mechanisms. Increased awareness among developers about supply chain risks can foster more secure coding practices.
Pessimistic Outlook
The stealthy nature and rapid evidence erasure of this malware pose a significant challenge for incident response and forensic analysis, potentially allowing attackers to maintain persistence undetected for extended periods. The use of compromised servers as LLM relays could facilitate further illicit activities, masking the true origin of AI requests.
Get the next signal in your inbox.
One concise weekly briefing with direct source links, fast analysis, and no inbox clutter.
More reporting around this signal.
Related coverage selected to keep the thread going without dropping you into another card wall.