LLM-Enabled Honeyport Monitors All 65535 TCP Ports
Sonic Intelligence
An experimental honeyport uses Linux networking to monitor all 65535 TCP ports.
Explain Like I'm Five
"Imagine you have a special house that has a door for every single number from 1 to 65535. This article talks about setting up such a house on the internet, so you can see who tries to knock on any of those doors, even the secret ones, to learn about bad guys trying to find open doors."
Deep Intelligence Analysis
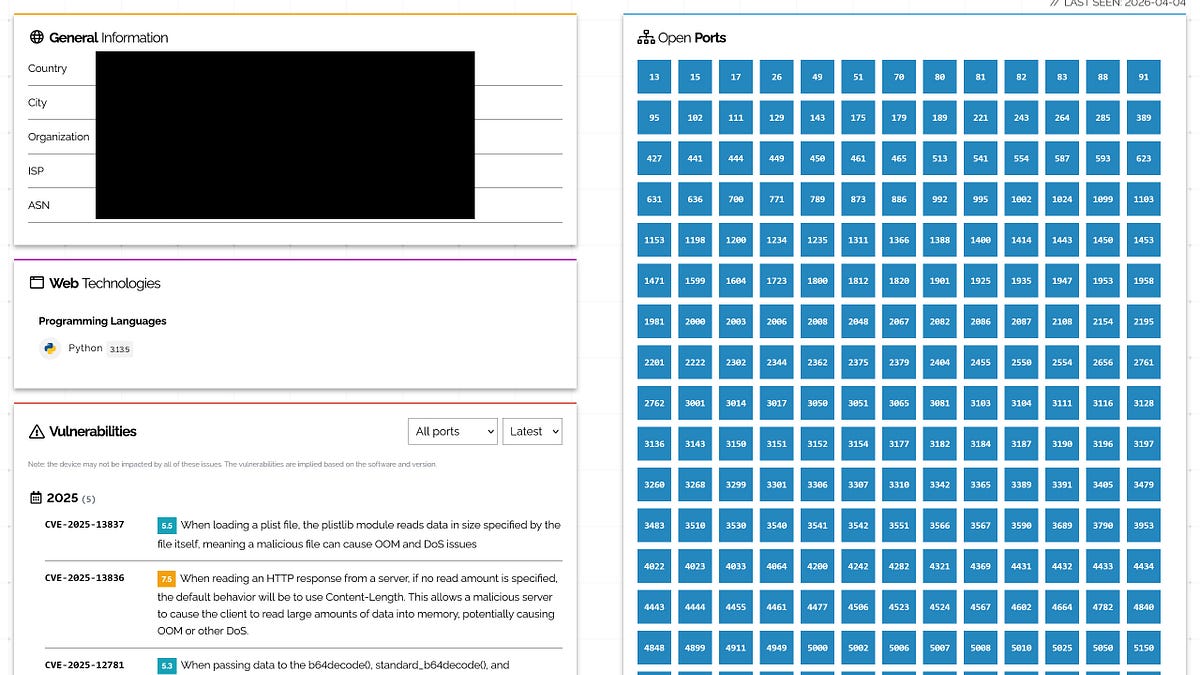
The setup meticulously details the use of `ip netns` for network namespace isolation, ensuring the experimental environment is contained and does not interfere with the host system. Incoming packets are redirected to a local listener on 127.0.0.1:1234, effectively creating a catch-all trap for network probes. While the article mentions the involvement of an LLM, the provided content primarily focuses on the intricate network configuration, leaving the specific role and integration of the LLM largely underexplored.
This technical demonstration offers valuable insights for cybersecurity researchers seeking to understand reconnaissance patterns and identify emerging threats. By observing traffic across the entire port spectrum, defenders can gain a more complete picture of attacker methodologies. However, the practical utility of this specific implementation for AI-driven security remains limited without further elaboration on the LLM's function. Future developments would need to clearly define how AI processes the intercepted data to extract actionable intelligence, moving beyond raw packet capture to automated threat analysis and response.
Visual Intelligence
flowchart LR
A[Public Internet] --> B[Network Interface];
B --> C[Network Namespace];
C --> D[DHCP Client];
C --> E[IP Forwarding];
E --> F[IPTables TPROXY];
F --> G[Local Listener];
Auto-generated diagram · AI-interpreted flow
Impact Assessment
Monitoring all ports on a public IP provides valuable intelligence on internet scanning activity and potential threats. This experimental setup demonstrates advanced Linux networking techniques for security research, offering insights into attacker methodologies and network reconnaissance patterns.
Key Details
- ● The setup leverages Linux `anyIP` and `transparent IP` features to bind a socket to all 65535 ports.
- ● An `iptables` TPROXY rule forwards all incoming TCP packets to a local listener on 127.0.0.1:1234.
- ● Network isolation for the experiment is achieved using `ip netns` (network namespaces) instead of Docker.
- ● The system is deployed on a residential public internet host to observe scanner attempts.
- ● The article mentions an LLM is involved but does not detail its specific role in the provided content.
Optimistic Outlook
This technique could enable highly comprehensive threat intelligence gathering, revealing novel attack vectors or scanner behaviors that target obscure ports. If the LLM integration were fully realized, it could automate the analysis of vast amounts of raw network traffic, making honeyports more effective and scalable for cybersecurity research.
Pessimistic Outlook
The complexity of managing such a broad port monitoring system could introduce its own security vulnerabilities if not meticulously configured, potentially turning the honeyport into an attack surface. Without clear elaboration on the LLM's role, the "AI" aspect remains a conceptual add-on, limiting its immediate practical impact on AI-driven security.
Get the next signal in your inbox.
One concise weekly briefing with direct source links, fast analysis, and no inbox clutter.
More reporting around this signal.
Related coverage selected to keep the thread going without dropping you into another card wall.