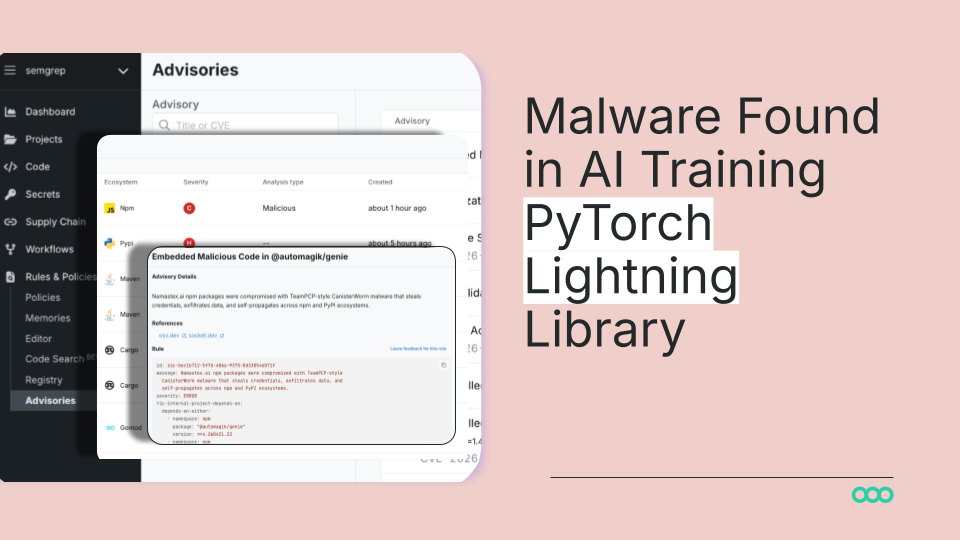
PyTorch Lightning Supply Chain Attack Steals Credentials, Poisons Repositories
Sonic Intelligence
A supply chain attack compromised PyTorch Lightning, stealing credentials and poisoning GitHub repositories.
Explain Like I'm Five
"Imagine if a bad guy snuck a secret, harmful toy into a popular box of building blocks that many people use to make cool robots. When you use those blocks, the bad toy secretly tries to steal your passwords and mess up your other robot projects, and then tries to spread to other people's blocks too."
Deep Intelligence Analysis
The attack leverages an obfuscated JavaScript payload within a hidden `_runtime` directory, activating automatically upon module import. Once executed, the malware systematically steals credentials, authentication tokens, environment variables, and cloud secrets. Its sophistication is further demonstrated by its multi-channel exfiltration mechanism, which includes HTTPS POSTs to a command-and-control server, a GitHub commit search dead-drop, and the creation of attacker-controlled public GitHub repositories. Furthermore, the malware exhibits worm-like propagation, leveraging npm publish credentials to inject droppers into other packages, thereby extending its reach across the software supply chain.
This incident underscores the escalating sophistication of attacks targeting open-source dependencies, posing a direct challenge to the trust model underpinning modern software development. For organizations leveraging PyTorch Lightning, immediate action is required, including scanning projects with tools like Semgrep, auditing repositories for injected files, and rotating any compromised credentials. The broader implication is a heightened need for proactive security measures, continuous dependency monitoring, and a re-evaluation of trust boundaries within the AI/ML open-source community to prevent future, potentially more devastating, supply chain compromises.
Visual Intelligence
flowchart LR A["Malicious Package"] --> B["Pip Install Lightning"] B --> C["Obfuscated JS Payload"] C --> D["Steal Credentials"] C --> E["Poison GitHub Repos"] D --> F["Exfiltrate Data"] E --> F F --> G["C2 Server / GitHub Dead-Drop"]
Auto-generated diagram · AI-interpreted flow
Impact Assessment
This attack highlights critical vulnerabilities in the AI development supply chain, threatening sensitive data and code integrity for numerous deep learning projects. It underscores the urgent need for robust security practices in open-source dependencies, impacting teams building image classifiers, LLMs, and diffusion models.
Key Details
- PyPI package 'lightning' versions 2.6.2 and 2.6.3 were compromised.
- The attack occurred on April 30, 2026, affecting a widely-used deep learning framework.
- Malware steals credentials, authentication tokens, environment variables, and cloud secrets.
- The malicious payload is obfuscated JavaScript, hidden in a '_runtime' directory, executing on module import.
- Exfiltration uses four parallel channels: HTTPS POST to C2, GitHub commit search dead-drop, and an attacker-controlled public GitHub repository.
- Worm propagation occurs through npm if publish credentials are found, injecting droppers into other packages.
Optimistic Outlook
Rapid detection and advisories from security firms like Semgrep enable developers to mitigate risks quickly, strengthening the overall security posture of the AI ecosystem through increased vigilance and improved tooling. This incident serves as a crucial lesson for enhancing supply chain security measures.
Pessimistic Outlook
The sophisticated, multi-channel exfiltration and worming capabilities suggest a persistent and advanced threat actor, potentially leading to widespread compromise across the AI/ML community before full remediation is achieved. The reliance on popular open-source libraries makes the attack surface vast and difficult to fully secure.
Get the next signal in your inbox.
One concise weekly briefing with direct source links, fast analysis, and no inbox clutter.
More reporting around this signal.
Related coverage selected to keep the thread going without dropping you into another card wall.