AI Agents Compromised in Critical NPM Supply Chain Attack
Sonic Intelligence
A critical npm supply chain attack compromised AI coding agents.
Explain Like I'm Five
"Imagine your smart robot helper that builds computer programs. Someone secretly put a bad toy in the box of building blocks it uses. When your robot picked up the building blocks, the bad toy instantly jumped out and started messing with your robot, all without anyone noticing for hours."
Deep Intelligence Analysis
The attack's efficacy was amplified by `axios`'s ubiquitous adoption, boasting 400 million monthly downloads and 174,000 direct dependents. The malicious versions, active for over three hours, were published after the lead maintainer's npm account was compromised, crucially lacking the OIDC Trusted Publisher provenance attestations that should have flagged them. The forensic link to the DPRK-affiliated UNC1069 group, via the WAVESHAPER backdoor, elevates this from a mere cybercrime event to a national security concern, indicating a deliberate targeting of development infrastructure that underpins critical AI capabilities. This incident underscores the urgent need for more robust, real-time verification mechanisms beyond simple account credentials.
Looking forward, this event necessitates a paradigm shift in how AI development environments are secured. Organizations must implement OS-level security proxies that scrutinize every package installation, irrespective of its source, and enforce strict provenance checks. The autonomous nature of AI agents demands a 'zero-trust' approach to external code, where every dependency is treated as a potential threat until verified. Failure to adapt will leave AI development pipelines perpetually exposed to similar, potentially more damaging, supply chain infiltrations, jeopardizing intellectual property and national technological advantage. This incident is a stark reminder that the security of AI begins at the foundational layer of its software supply chain.
metadata: {"ai_detected": true, "model": "Gemini 2.5 Flash", "label": "EU AI Act Art. 50 Compliant"}
_Context: This intelligence report was compiled by the DailyAIWire Strategy Engine. Verified for Art. 50 Compliance._
Visual Intelligence
flowchart LR A["Attacker Compromises Account"] --> B["Publish Malicious Axios"] B --> C["AI Agent Runs npm install"] C --> D["RAT Executes Instantly"] D --> E["System Compromised"] E --> F["C2 Beaconing"] F --> G["Remote Control"]
Auto-generated diagram · AI-interpreted flow
Impact Assessment
This incident exposes a critical vulnerability in the software supply chain, specifically targeting autonomous AI development agents. The rapid, silent compromise of widely used packages poses a significant threat to development environments and intellectual property, demanding immediate re-evaluation of automated security protocols.
Key Details
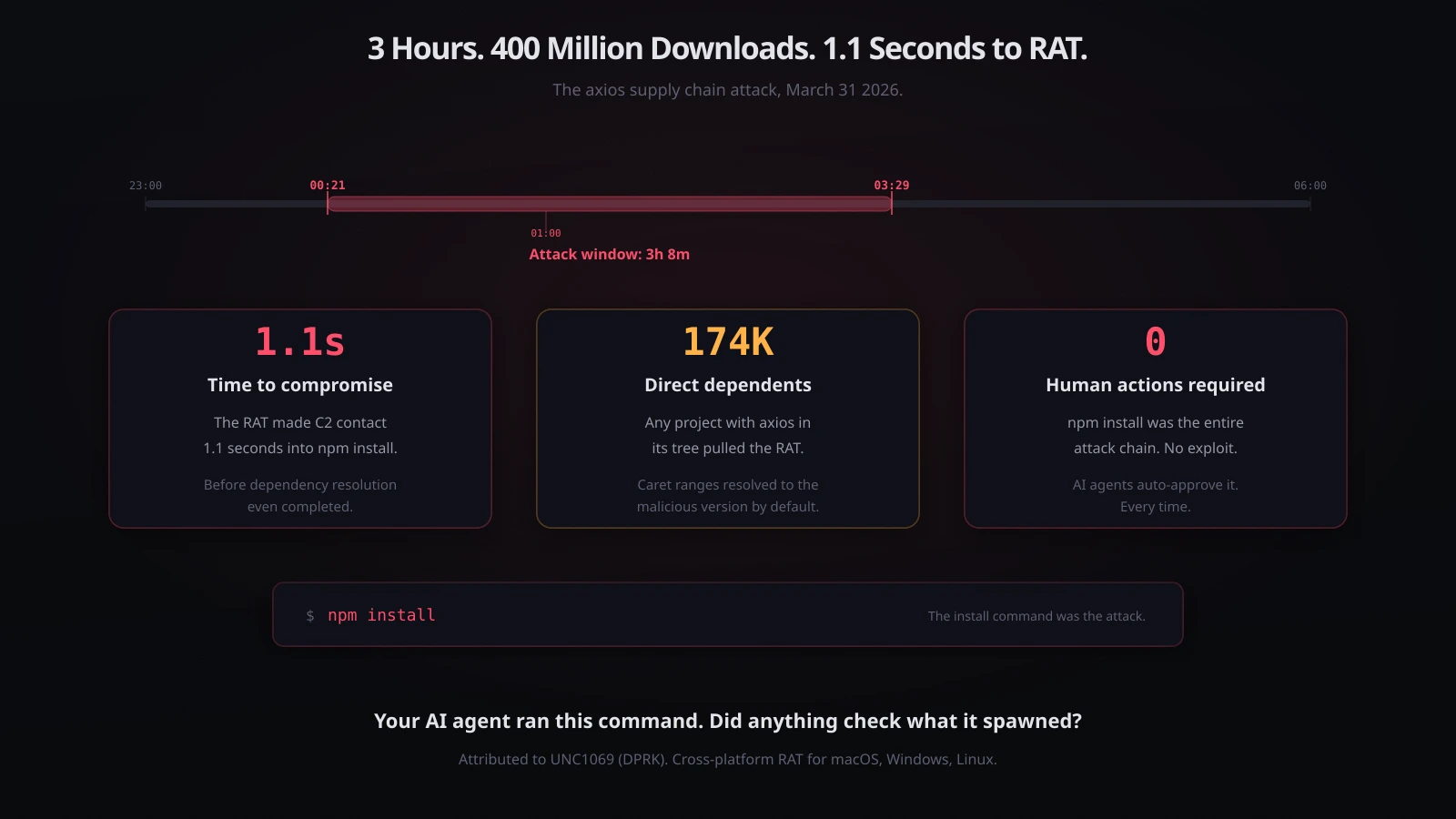
- Malicious `axios` versions (1.14.1, 0.30.4) were active for 3 hours and 8 minutes on March 31, 2026.
- The attack deployed a cross-platform Remote Access Trojan (RAT) on macOS, Windows, and Linux systems.
- The RAT executed 1.1 seconds into `npm install`, bypassing dependency resolution checks.
- `axios` is downloaded 400 million times monthly and has 174,000 direct dependents.
- The macOS RAT variant shows overlap with WAVESHAPER, attributed to DPRK-linked UNC1069.
Optimistic Outlook
The incident could catalyze the development and widespread adoption of advanced OS-level security proxies for AI agents, alongside enhanced provenance attestation requirements for package registries. This could lead to a more resilient and verifiable software supply chain, ultimately strengthening the security posture of AI development workflows.
Pessimistic Outlook
The autonomous nature of AI agents, constantly executing routine commands like `npm install`, creates a persistent and difficult-to-monitor attack surface. This vulnerability could be exploited by more sophisticated, stealthy supply chain attacks, leading to widespread compromises that are challenging to detect and mitigate, eroding trust in automated development processes.
Get the next signal in your inbox.
One concise weekly briefing with direct source links, fast analysis, and no inbox clutter.
More reporting around this signal.
Related coverage selected to keep the thread going without dropping you into another card wall.




