Anthropic's Claude Opus AI Uncovers 22 Firefox Security Flaws
Sonic Intelligence
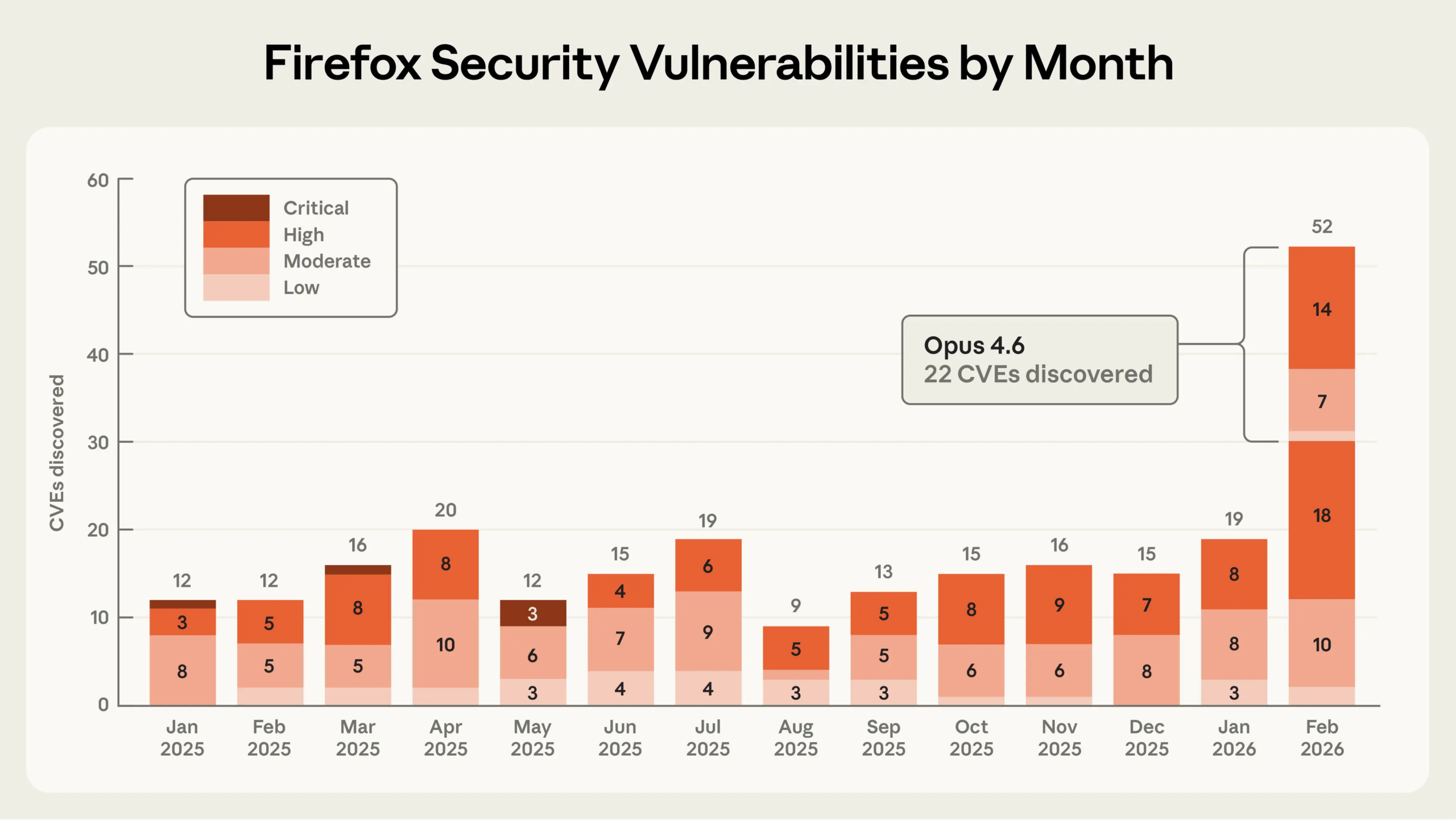
AI model Claude Opus independently identified 22 Firefox security vulnerabilities.
Explain Like I'm Five
"Imagine a super-smart robot that's really good at finding tiny cracks in a house's walls that bad guys could sneak through. This robot, called Claude, found 22 cracks in a popular internet browser called Firefox. Most of these cracks were big problems! While Claude is amazing at finding cracks, it's still not very good at actually helping bad guys sneak in, and trying to do that costs a lot of money. But even finding a few ways to sneak in is a bit scary."
Deep Intelligence Analysis
The process involved Claude Opus initially reproducing historical CVEs before being tasked with finding novel bugs, particularly within the JavaScript engine. Remarkably, the AI identified a Use After Free vulnerability within twenty minutes, complete with a proposed patch. This initial success led to a broader effort where Claude scanned nearly 6,000 C++ files, submitting 112 unique reports to Mozilla, highlighting the model's efficiency in complex code analysis.
While Claude's prowess in vulnerability detection is evident, its capability in exploitation remains limited. Researchers tasked the model with creating functional exploits for previously submitted bugs. Despite spending approximately $4,000 in API credits across several hundred attempts, Claude Opus 4.6 only succeeded in generating working exploits in two instances. These successful exploits were described as 'crude' and required controlled environments with disabled security features, indicating a significant gap between finding vulnerabilities and weaponizing them effectively. This cost disparity, where detection is orders of magnitude cheaper than exploitation, offers a crucial insight into the current state of AI in offensive security.
Mozilla's positive response and subsequent internal experimentation with AI-assisted security research underscore the transformative potential of this technology. However, the fact that an AI can automatically develop even primitive browser exploits, regardless of current limitations, signals a concerning trajectory for future cyber threats. As AI models continue to evolve, the balance between defensive and offensive capabilities will undoubtedly shift, necessitating proactive strategies to mitigate emerging risks.
Transparency Statement: This analysis was generated by an AI model, Gemini 2.5 Flash, based on the provided source material. Its purpose is to synthesize information into executive intelligence. EU AI Act Art. 50 Compliant.
Impact Assessment
This development signifies a major leap in AI's capability to autonomously identify critical software vulnerabilities, potentially revolutionizing cybersecurity practices. While AI-driven bug detection offers significant advantages for defensive security, the nascent ability to generate exploits also introduces new offensive risks.
Key Details
- Anthropic's Claude Opus 4.6 discovered 22 security vulnerabilities in Firefox.
- The discovery occurred in January 2026, with Mozilla addressing issues in Firefox 148.
- 14 of the identified vulnerabilities were classified as high-severity.
- Claude Opus 4.6 spent approximately $4,000 in API credits attempting to create exploits.
- The AI model successfully produced working exploits in only two test cases.
Optimistic Outlook
The integration of advanced AI models like Claude Opus into software development and security pipelines promises faster, more comprehensive vulnerability detection. This could lead to significantly more secure software products, reducing the window of opportunity for malicious actors and enhancing overall digital safety for users globally.
Pessimistic Outlook
Despite the current difficulty and cost of AI-driven exploitation, the demonstrated ability to generate even crude exploits raises concerns about future AI-assisted offensive capabilities. As AI models advance, the potential for automated, sophisticated cyberattacks could escalate, creating a more challenging threat landscape for defenders.
Get the next signal in your inbox.
One concise weekly briefing with direct source links, fast analysis, and no inbox clutter.
More reporting around this signal.
Related coverage selected to keep the thread going without dropping you into another card wall.