ClawGate: Capability-Based File Access for Isolated AI Agents
Sonic Intelligence
ClawGate offers scoped, time-limited, and audited file access for AI agents, enhancing security by preventing full filesystem exposure.
Explain Like I'm Five
"Imagine your AI is like a kid who needs to borrow your toys. Instead of giving them the keys to the whole house, you only give them a key to the toy box for a little while, and you watch what they play with."
Deep Intelligence Analysis
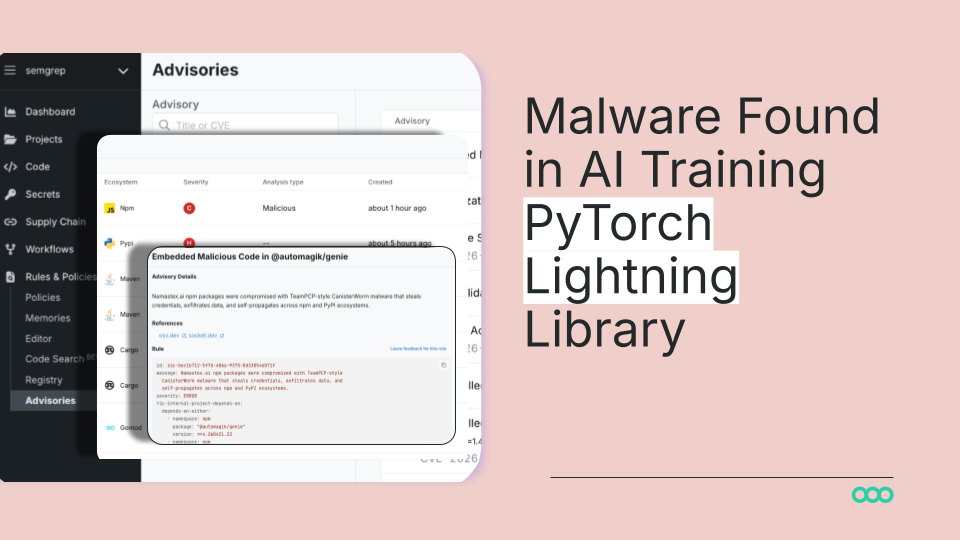
The system incorporates multiple layers of defense, including end-to-end encryption, forward secrecy, and signed JWT tokens. It also enforces path safety by canonicalizing paths, rejecting symlinks, and preventing traversal. Furthermore, it hardcodes blocks on sensitive directories, ensuring they are never accessible to agents.
ClawGate's design emphasizes ease of use, with a one-line installation and hot-reload token functionality. This lowers the barrier to adoption, making it more likely that developers will integrate it into their workflows. The audit trail provides valuable insights into agent activity, enabling security teams to detect and respond to suspicious behavior. The compatibility with CLI-based agents and MCP servers extends its applicability to various AI deployment scenarios.
However, the effectiveness of ClawGate hinges on responsible usage. Overly permissive access grants or inadequate monitoring of audit logs could negate its security benefits. Continuous evaluation and refinement of access policies are essential to maintain a strong security posture. The project's commitment to defense in depth and a zero-trust approach aligns with industry best practices for securing AI systems.
Impact Assessment
As AI agents become more prevalent, securing their access to sensitive data is crucial. ClawGate addresses this by providing a secure, auditable, and scoped access control mechanism, mitigating the risks associated with compromised AI agents.
Key Details
- ClawGate uses X25519 + XChaCha20-Poly1305 end-to-end encryption for transport security.
- It employs Ed25519 signed JWT capability tokens for authentication.
- The system logs every operation with path, timestamp, and result for auditing.
- ClawGate blocks access to sensitive paths like ~/.ssh, ~/.aws, and ~/.gnupg.
Optimistic Outlook
ClawGate's approach could lead to more secure AI deployments, fostering greater trust and adoption. Its ease of installation and hot-reload token feature simplifies security management, encouraging wider use among developers.
Pessimistic Outlook
Despite its security features, ClawGate's effectiveness depends on proper configuration and adherence to security best practices. A false sense of security could arise if users fail to adequately scope access or monitor audit logs, potentially leading to breaches.
Get the next signal in your inbox.
One concise weekly briefing with direct source links, fast analysis, and no inbox clutter.
More reporting around this signal.
Related coverage selected to keep the thread going without dropping you into another card wall.