North Korean Agents Leverage AI for Sophisticated Remote Hiring Scams, Microsoft Warns
Sonic Intelligence
North Korean state-backed agents are using AI, including deepfakes and voice changers, to secure remote IT jobs in Western firms.
Explain Like I'm Five
"Bad guys from North Korea are using clever computer tricks, like making their voices sound different or changing faces in pictures, to pretend they are someone else and get jobs at companies far away. They send the money they earn back to their country."
Deep Intelligence Analysis
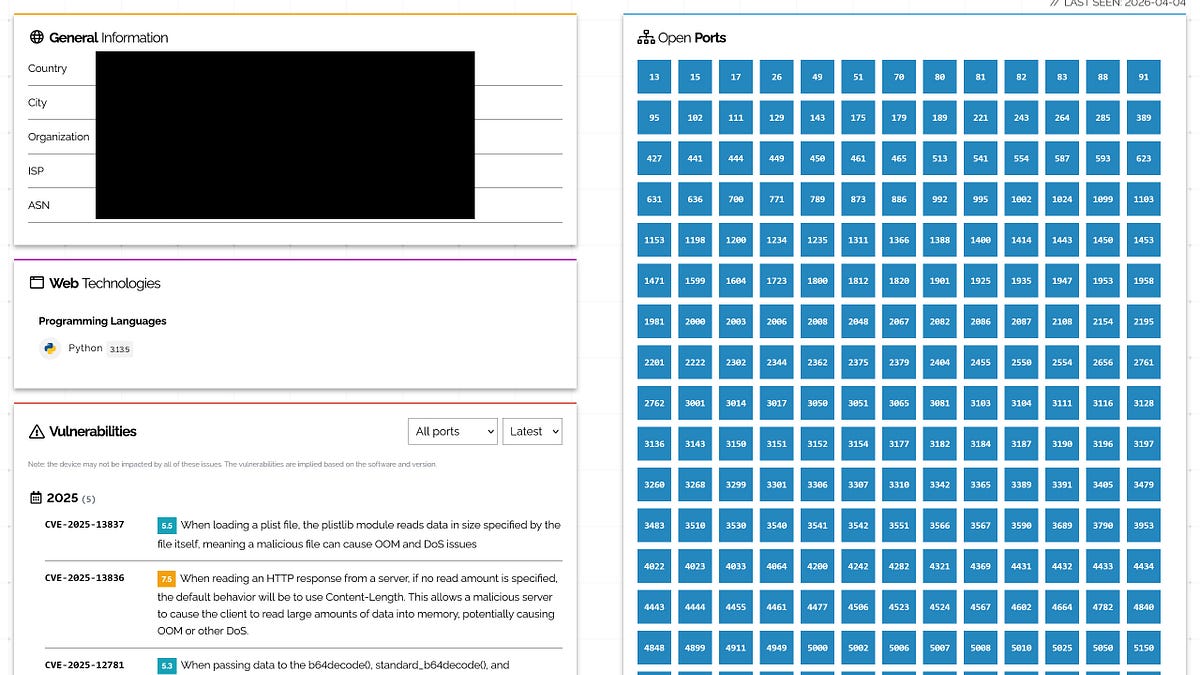
The core of the scam involves fraudsters applying for remote IT and software development positions using fabricated identities. AI plays a crucial role across the entire attack lifecycle. For initial application stages, AI platforms are leveraged to generate "culturally appropriate" name lists and corresponding email address formats, creating highly credible false personas. An example prompt cited by Microsoft was "create a list of 100 Greek names," illustrating the precision with which these identities are crafted.
During the interview process, the North Korean agents employ voice-changing software to mask their accents, enabling them to convincingly pass as Western candidates. Furthermore, AI applications like Face Swap are utilized to insert the faces of North Korean IT workers into stolen identity documents and to generate "polished" headshots for CVs, enhancing the visual credibility of their fake profiles. This level of AI-driven manipulation makes it exceedingly difficult for traditional human-led verification processes to detect fraud.
Beyond identity fabrication, AI is also used strategically to improve the success rate of applications. Scammers employ AI to scour job postings on platforms like Upwork, extracting skill requirements to tailor their applications more effectively. Once hired, AI continues to assist them in maintaining their cover, being used to write emails, translate documents, and even generate code, helping them stave off detection for poor performance or fraud.
The implications of these tactics are severe, ranging from financial losses for companies to the potential theft of sensitive data and intellectual property, and even national security risks. Microsoft's previous actions, such as disrupting 3,000 Outlook or Hotmail accounts linked to these activities, underscore the scale of the problem. In response, Microsoft advises companies to conduct job interviews for IT workers via video or in person, and to train interviewers to spot "tells" of deepfake videos or images, such as pixellation inconsistencies or unnatural light interaction with AI-generated faces. This incident highlights the urgent need for enhanced cybersecurity measures and advanced AI detection capabilities in hiring and identity verification processes.
Impact Assessment
This highlights a critical and evolving cybersecurity threat where nation-state actors exploit AI to bypass traditional hiring security measures. It underscores the dual-use nature of AI and the urgent need for companies to adapt their verification processes against sophisticated digital deception.
Key Details
- North Korean groups Jasper Sleet and Coral Sleet use AI for hiring scams.
- AI tools include voice-changing software and Face Swap for identity alteration.
- AI generates "culturally appropriate" names and email formats for fake identities.
- Scammers use AI to analyze job postings and tailor applications.
- Microsoft disrupted 3,000 Outlook/Hotmail accounts linked to these activities last year.
Optimistic Outlook
Increased awareness from reports like Microsoft's can prompt companies to implement more robust AI-detection tools and verification protocols in hiring. This could lead to the development of advanced countermeasures that not only thwart these specific scams but also enhance overall digital identity security.
Pessimistic Outlook
The sophisticated use of AI by state-backed actors suggests an escalating arms race in digital deception, making it increasingly difficult for companies to discern genuine applicants from fraudulent ones. This could lead to significant financial losses, intellectual property theft, and national security risks if not effectively countered.
Get the next signal in your inbox.
One concise weekly briefing with direct source links, fast analysis, and no inbox clutter.
More reporting around this signal.
Related coverage selected to keep the thread going without dropping you into another card wall.