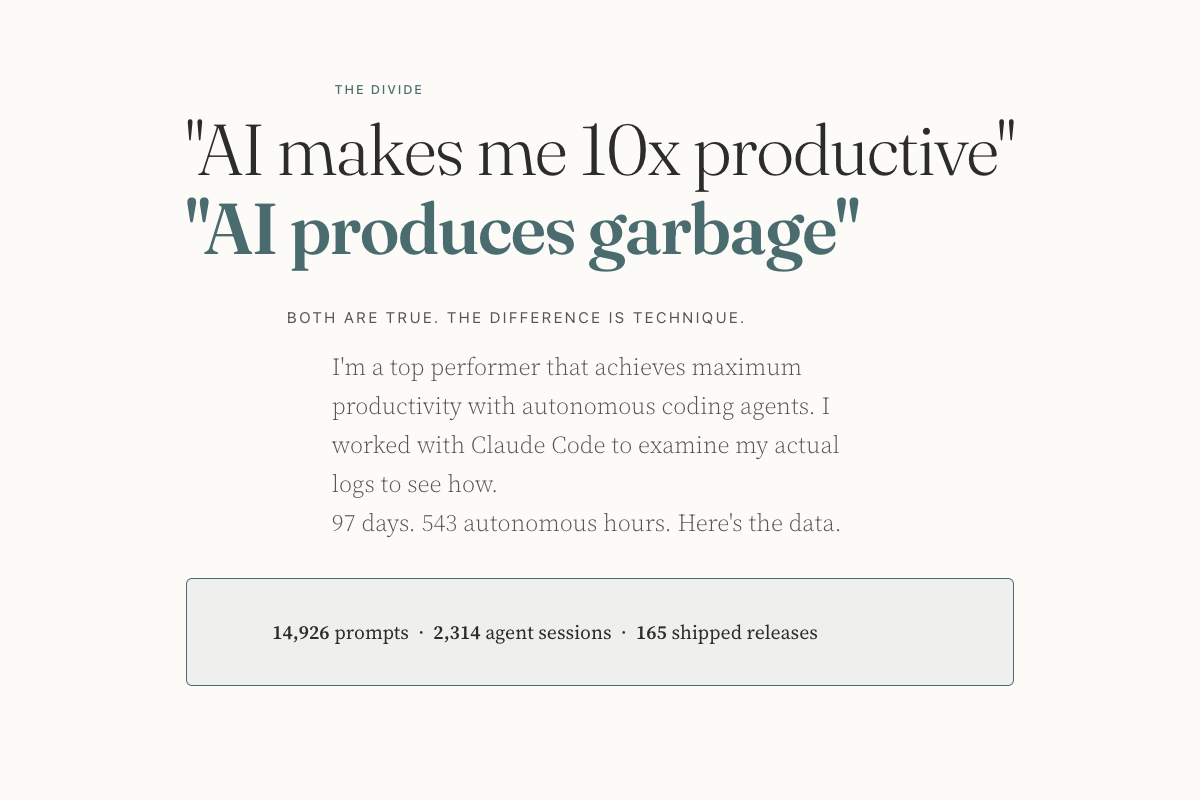
Rigor Proxy Fights AI 'Enshittification' with Local Policy Enforcement
Sonic Intelligence
Rigor acts as a local MITM proxy, enforcing policies to prevent AI agent 'enshittification'.
Explain Like I'm Five
"Imagine your AI helper sometimes says silly things or tries to sell you stuff. Rigor is like a special filter on your computer that checks everything your AI says *before* it gets to you, making sure it's helpful and not annoying, all without sending your secrets anywhere."
Deep Intelligence Analysis
Unlike existing guardrail solutions such as Guardrails AI or NeMo Guardrails, which typically function as libraries integrated within the application, Rigor's network-level interception provides a distinct advantage: zero-integration overhead for the AI agent itself. By routing an agent's network traffic through Rigor, policies are automatically applied, leveraging a local CA to decrypt, inspect, and re-encrypt TLS traffic. The core of its policy engine is `regorus`, a Rust implementation of OPA's Rego language, enabling highly granular and auditable constraint evaluation directly on the user's machine. This local execution model, explicitly designed with no telemetry or phone-home functionality, addresses paramount data privacy and security concerns, ensuring that sensitive code or LLM interactions never leave the local environment. Performance metrics indicate minimal latency, typically under 20ms for inspection, making it viable for interactive agent use cases.
This paradigm of external, network-based AI policy enforcement could redefine the security and reliability landscape for AI agents. It empowers organizations to establish consistent behavioral standards across heterogeneous AI tools and models without requiring deep modifications to each agent's codebase. The open-source nature of Rigor (MIT license) further encourages community-driven development of policy packs, potentially leading to a robust ecosystem of shared best practices for agent governance. Looking ahead, the widespread adoption of such proxy-based solutions might become a de facto standard for ensuring compliance, mitigating risks, and fostering responsible AI development, particularly as agents gain more autonomy and access to critical systems. The ability to inject "rigor" into AI agent interactions at the network layer provides a powerful new lever for ensuring their outputs are not just intelligent, but also trustworthy and aligned with user intent.
Visual Intelligence
flowchart LR A["AI Agent"] --> B["Rigor Intercept"] B --> C["Decrypt / Inspect"] C --> D["Apply Rego Policy"] D --> E["Re-encrypt / Forward"] E --> F["LLM API"]
Auto-generated diagram · AI-interpreted flow
Impact Assessment
Rigor addresses a critical challenge in AI agent deployment by offering a universal, network-level mechanism to control agent behavior and prevent undesirable outputs. This approach allows developers and users to enforce custom policies, enhancing the reliability and trustworthiness of AI interactions without modifying core agent code.
Key Details
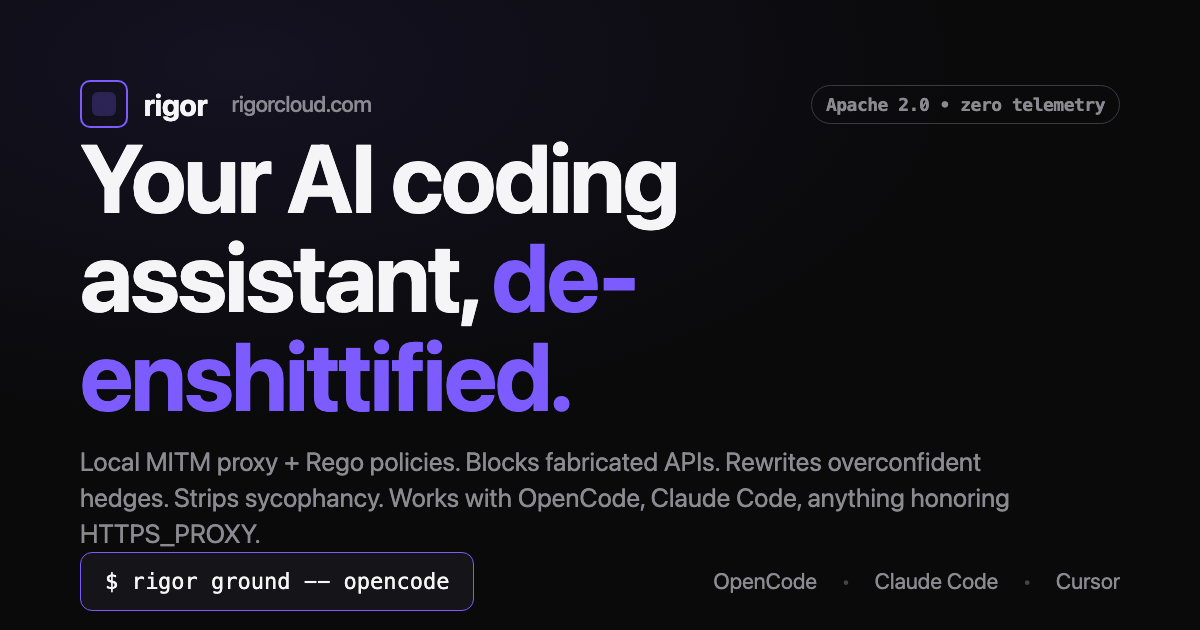
- Rigor operates as a local Man-in-the-Middle (MITM) proxy for AI agent traffic.
- It uses a local CA to decrypt, inspect, and re-encrypt TLS traffic, ensuring data stays on the laptop.
- Constraint evaluation is performed locally via the `regorus` engine, a Rust subset of OPA's Rego policy language.
- The tool is open source under an MIT license, with binaries signed and publicly available.
- Supports OpenCode and Claude Code, with macOS (arm64 + x86_64) currently available and Linux/Windows on the roadmap.
Optimistic Outlook
This approach offers a powerful new layer of control for AI agent deployment, fostering greater trust and predictability in AI interactions. By enabling custom, local policy enforcement, Rigor could accelerate the adoption of autonomous agents in sensitive applications, allowing for tailored behavior without modifying core LLM models.
Pessimistic Outlook
Implementing a local MITM proxy introduces potential complexity and overhead for users, requiring trust in the proxy's security and certificate management. While local, any vulnerability in Rigor itself could expose sensitive LLM traffic, and the need for custom Rego policies for advanced use might deter less technical users.
Get the next signal in your inbox.
One concise weekly briefing with direct source links, fast analysis, and no inbox clutter.
More reporting around this signal.
Related coverage selected to keep the thread going without dropping you into another card wall.