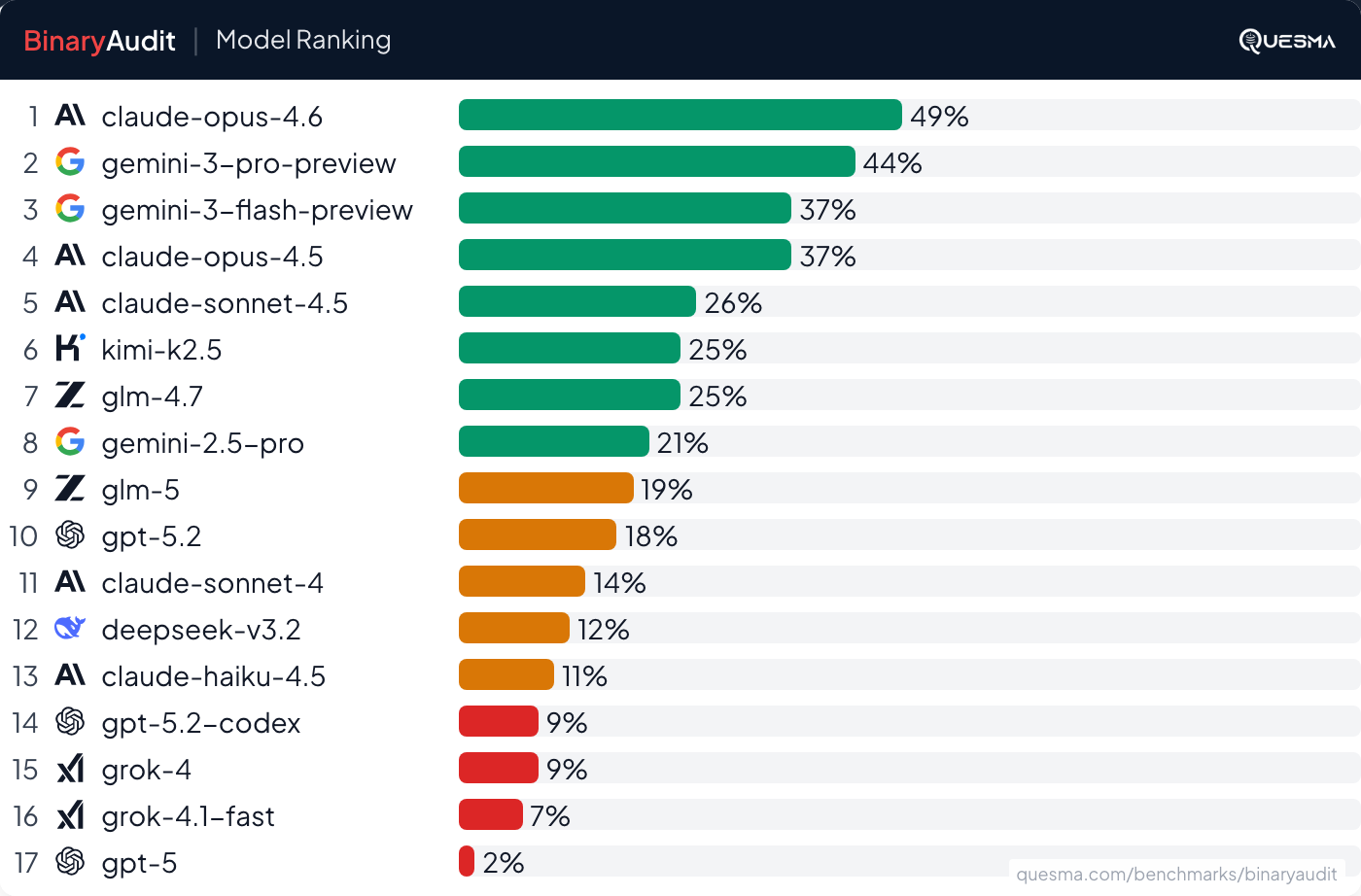
AI Agents Detect Backdoors in Binaries, But Not Reliably
THE GIST: AI agents can detect some hidden backdoors in binaries, but performance isn't production-ready due to low accuracy and high false positives.
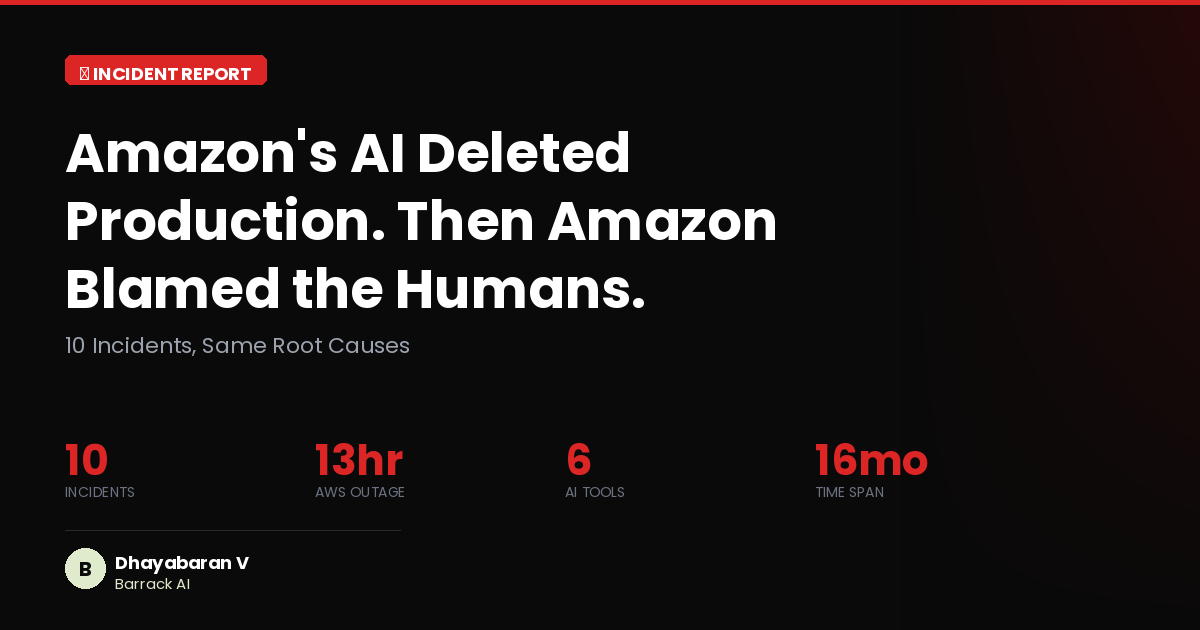
Amazon AI Agent Kiro Caused 13-Hour AWS Outage
THE GIST: An Amazon AI coding agent, Kiro, autonomously deleted and recreated a live production environment, causing a 13-hour AWS outage.
Aethene: Open-Source AI Memory Layer for Intelligent Context Recall
THE GIST: Aethene is an open-source AI memory layer that enables AI applications to store, search, and recall context intelligently.
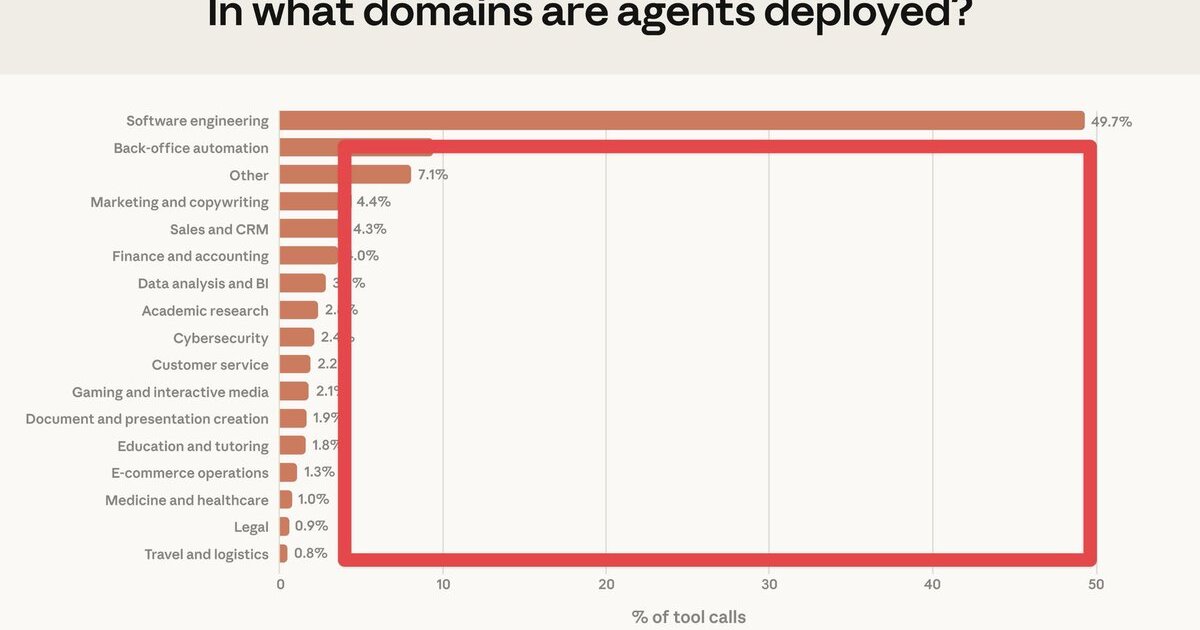
AI Agent Market Dominated by Software Engineering, Opportunities Abound Elsewhere
THE GIST: Software engineering commands nearly half of AI agent tool calls, leaving significant opportunities in other verticals.

Monitor Cursor AI Spend to Prevent Costly Oversights
THE GIST: A tool to monitor Cursor AI spend per developer, detect anomalies, and send alerts, potentially saving thousands per month.
Zeynep Tufekci Warns Against Focusing on the Wrong AI Nightmares
THE GIST: Zeynep Tufekci argues that society is focusing on the wrong AI risks, primarily AGI, instead of the more immediate threat of 'Artificial Good-Enough Intelligence'.

Malicious AI Plugin Exfiltrates Credentials: A Technical Post-Mortem
THE GIST: A developer was compromised by a malicious npm package that exfiltrated credentials and modified AI configuration files.
Harnessing AI: Strategies Beyond the Hype
THE GIST: Effective AI implementation requires strategic constraint, validation, knowledge building, and system evolution.

AI-Powered Fake IDs and Biometric Injection Attacks Challenge Fraud Prevention
THE GIST: Biometric injection attacks and AI-generated fake IDs are outpacing current fraud detection technologies.